OVERVIEW
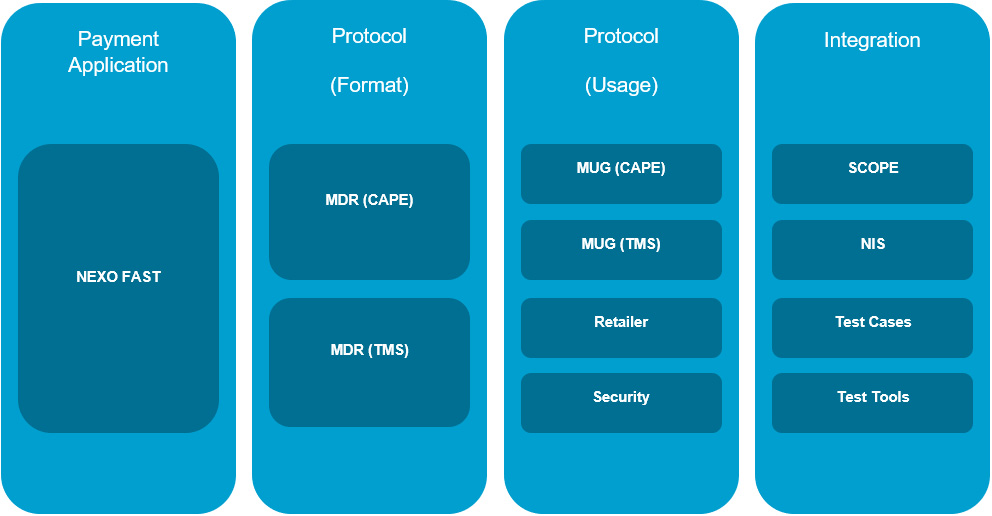
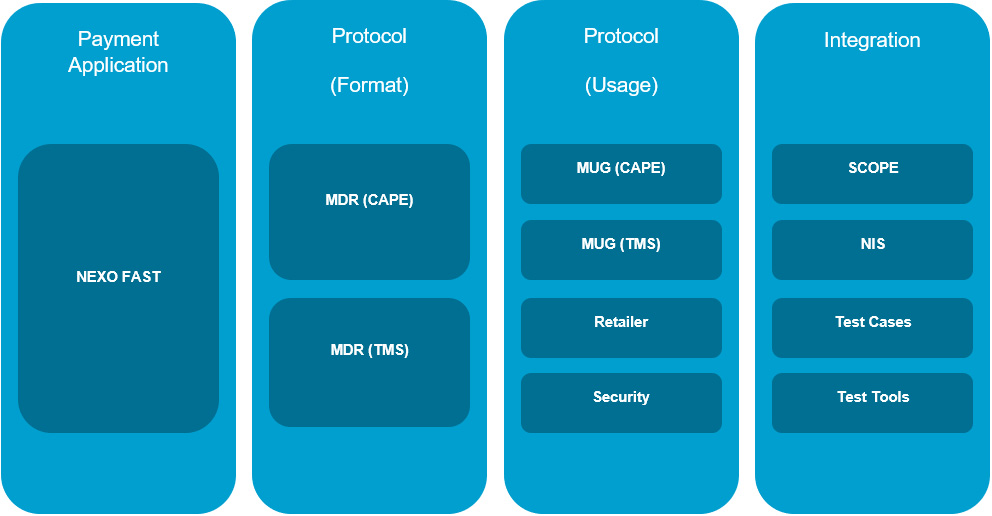
NIS v4.0 provides how to integrate the nexo Specifications and Protocols with a compliant nexo FAST payment application.
NIS v4.0 Package include the following nexo Specifications and Protocols:
- nexo Functional Scope
- nexo FAST v3.1 + Bulletins
- Bulletin 1 - Update on Technology Selection for handling a restart
- Bulletin 2 - Update on Card Product Selection for handling BIN ranges
- Bulletin 4 - IF Regulation Updates
- Bulletin 5 - Pre-Authorisation Service Updates
- nexo Acquirer v6.0
- nexo TMS v6.0
- nexo Retailer v3.1 (optional)
- nexo Security v2.0
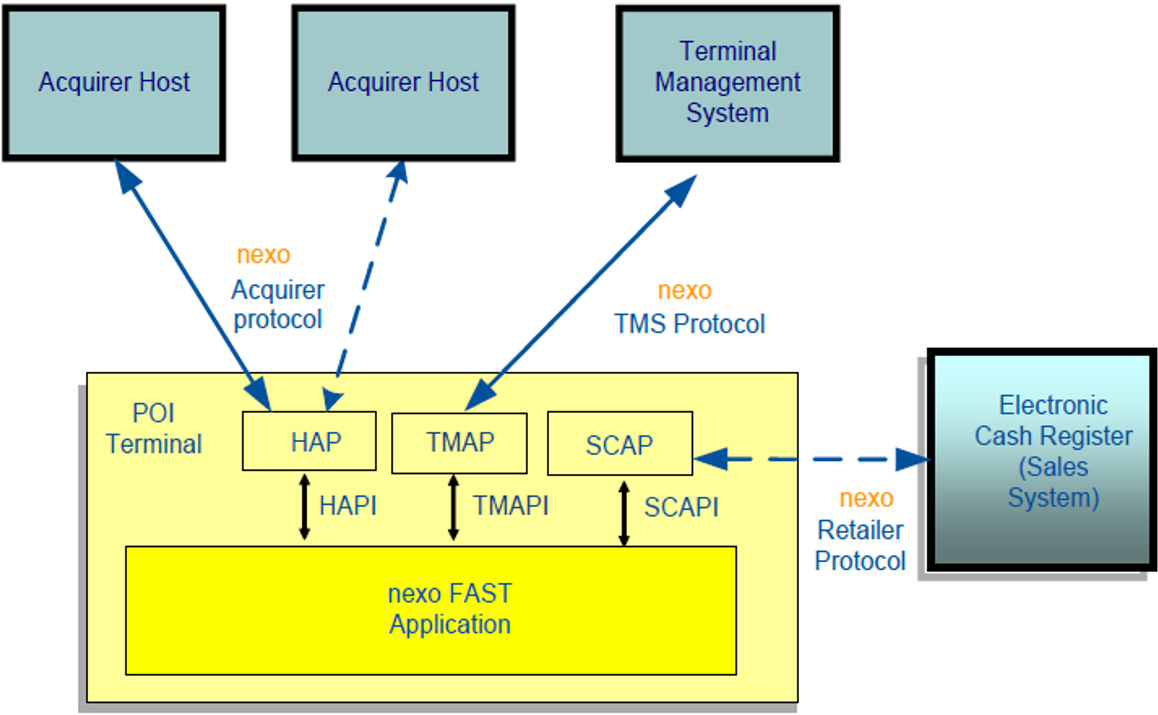
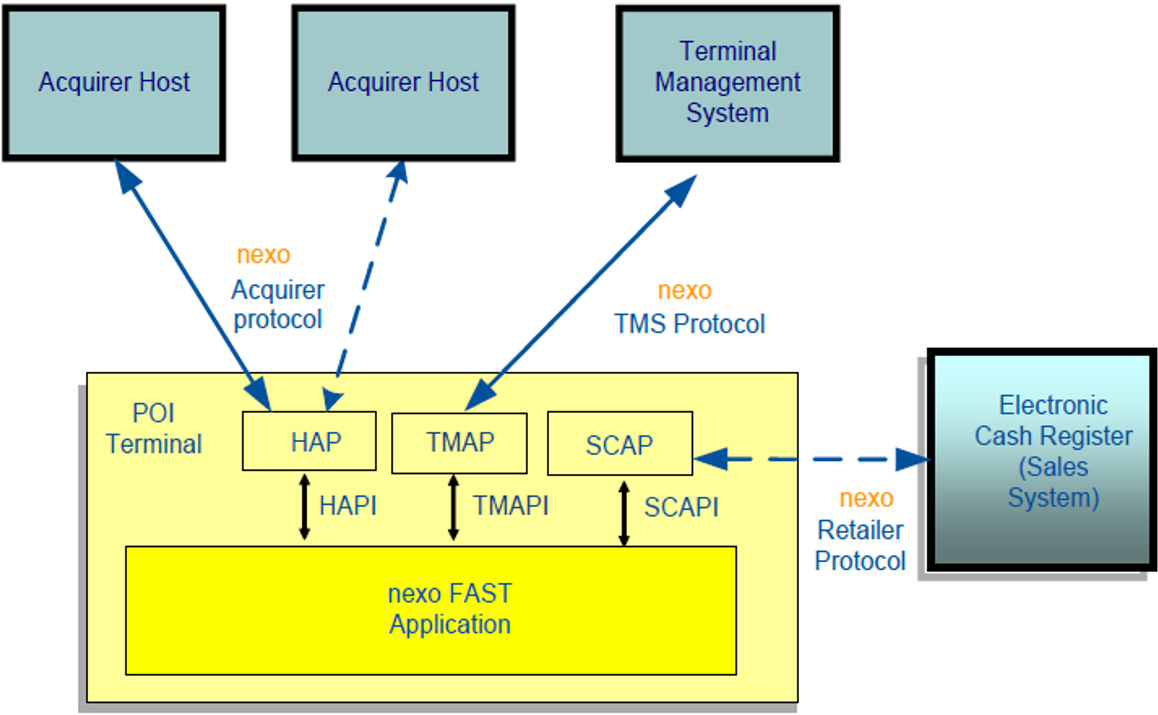
It describes, within the framework of a nexo implementation project, the following:
 |
The functions of the host acquirer interface application (HAP) with detailed description of the messages and data elements when the nexo FAST application has to interact with the nexo Acquirer protocol |
 |
An interface application for the terminal management system (TMAP) with detailed description of the messages and data elements used for configuration and maintenance purposes when the nexo FAST application has to interact with the nexo TMS protocol; |
 |
The interaction between the sale system and the dedicated interface (SCAP) using the nexo Retailer protocol when it has
to interact with the payment point of interaction (POI). |
NIS v4.0 FUNCTIONAL SCOPE
NIS v4.0 main objectives are as follows:
- To prove that POIs, based on nexo FAST payment application and nexo Acquirer/TMS Systems, work together,
- To prove the interoperability between all POIs, all Acquirers and TMS providers implementing nexo specifications and protocols
A nexo IS infrastructure is made up of a standalone or an integrated POI system communicating with:
- one or several Acquirer host(s) to process a card payment transaction,
- a Terminal Management System host for management functions, e.g. parameter download,
- a Sale System (optional).
NIS V4 PACKAGE FEATURES & SERVICES
| List of Features / Service |
| FEATURES SUPPORTED IN NIS V4.0 |
| CARD SERVICES |
| PAYMENT SERVICES |
| Payment |
| Refund (partial or total) |
| Cancellation |
| Pre-Authorisation (Reservation for nexo Retailer) |
| Pre-Authorisation |
| Update Pre-Authorisation |
| Completion |
| Deferred Payment |
| ADDITIONAL FEATURES |
| Payment with increased Amount |
| Payment with Cashback |
| Payment with voice authorisation |
| CARD MANAGEMENT SERVICES |
| ISO-4 PIN Format Support |
| AES DUKPT Support for Data Encipherment |
| ACCEPTANCE TECHNOLOGIES |
| Chip with Contact |
| Magnetic Stripe |
| Chip/Mobile/Wearable/Contactless |
| Manual Entry by Acceptor |
| Stored Card Data (stored by the Acceptor) |
| CARDHOLDER ENVIRONMENTS |
| Physical Card |
| Consumer Device |
| ACCEPTANCE ENVIRONMENTS |
| Physical POI |
| Attended |
| Unattended |
| Semiattended |
| CARDHOLDER VERIFICATION METHODS |
| EMV Offline Plaintext PIN |
| EMV Offline Enciphered PIN |
| Online PIN |
| Signature |
| No CVM Required |
| Offline Mobile Code |
| CARD AUTHENTICATION METHODS |
| EMV Offline DDA |
| EMV Offline CDA |
| EMV Offline fDDA |
| EMV Online Authentication |
| Static Authentication (CSC) |
| PAYMENT APPLICATION FUNCTIONS |
| Configuration |
| Transaction Initialisation |
| Language Selection |
| Technology Selection |
| Selection of the Application |
| Selection of the Brand / Within the Card |
| Card Data Retrieval (Token Request) |
| Card Authentication |
| Cardholder Verification |
| Authorisation |
| Referral |
| Completion |
| Reversal |
| Data Capture |
| Authorisation |
| Online |
| Offline |
| Batch |
| Batch Suspended Transaction |
| ADMINISTRATIVE SERVICES |
| Reconciliation |
| Diagnostic |
| Transaction Advice |
| DEVICE SERVICES |
| Print |
| Display |
| Sound |
| Input |
| SYSTEM SERVICES |
| Events notifications |
| Error management |
| Diagnosis |
| CARD SCHEMES |
| MasterCard Contactless |
| Visa VCPS |
| Amex ExpressPay |
| ESTATE MANAGEMENT FUNCTIONS |
| Service Configuration |
| Host Configuation |
| MAC |
| Retail CBC MAC with Hash |
| SHA2-256 |
Download NIS v4.0 Package
IMPLEMENTATION
An implementer of nexo specifications and protocols would require the following:
A POI Implementation
A Vendor implementing a nexo FAST POI terminal has to support
- A nexo FAST Application, Version 3.1 and Bulletins 1,2,4 and 5;
- An interface to the Host Acquirer Protocol responsible for handling the nexo Acquirer protocol v6.0;
- An interface to the Terminal Manager responsible for handling the nexo TMS protocol v6.0;
- Connections to at least one Acquirer Host in the operational environment. However, the POI shall support a multi acquirer environment;
- Connection to at least one TMS Host for the purpose of parameters downloads;
- Cryptographic mechanisms described in nexo Security specification v2.1;
- Optionally, an interface to the sales system responsible for handling the nexo Retailer protocol v3.1;
AN ACQUIRER IMPLEMENTATION
An acquirer implementing the nexo Acquirer protocol has to support
- The nexo Acquirer protocol v6.0;
- The cryptographic mechanisms described in nexo Security specification v2.1;
- The nexo TMS protocol v6.0, if the acquirer is also the Terminal Manager as well.
A TERMINAL MANAGER IMPLEMENTATION
A Terminal Manager Provider implementing the nexo TMS protocol has to support
- The nexo TMS protocol v6.0
- The cryptographic mechanisms described in nexo Security specification v2.1
CRYPTOGRAPHIC MECANISMS & KEY MANAGEMENT
The following cryptographic mechanisms & key management described in nexo Security specification v2.1 has to be supported:
- DUKPT as key derivation mechanism for PIN Encryption, Card Data Encryption and MAC protection;
- The Triple-DES algorithm for PIN and Card Data Encryption;
- Retail-CBC-MAC with SHA-256 for Message Authentication Code (MAC);
- Key download via TMS protocol is optional. Key download, requires asymmetric cryptography if implemented. If the TMS protocol is not used for key download, then keys are loaded locally in the POI or by other means.
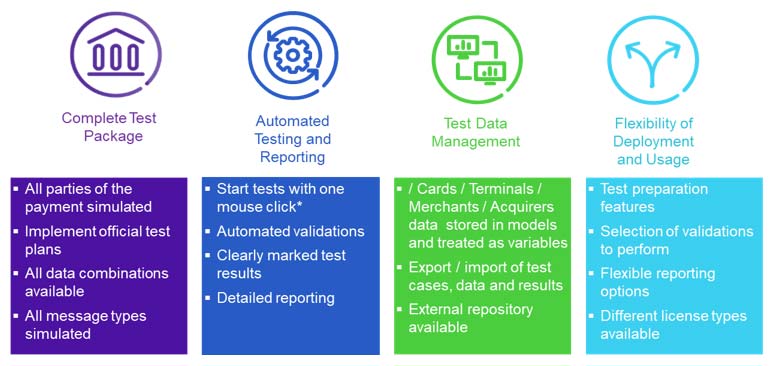
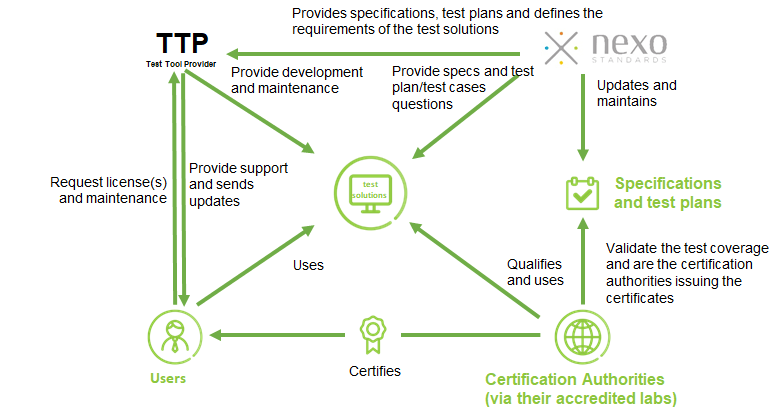
TEST TOOLS / VALIDATION
nexo standards has developed a suite of test tools that allows vendors, acquirers and processors to test the compliance of their payment systems and devices with nexo’s payment acceptance messaging standards and specifications, significantly reducing time to service launch and minimizing unexpected delays during the certification process.
The goal of the standards are to enable fast, interoperable and borderless payment acceptance by “standardising the exchange of payment acceptance data between merchants, acquirers, payment service providers and other payment stakeholders”.

CURRENT TEST TOOLS IS BASED ON NIS V4.0
What is nexo NIS V4.0 Test Solution
- Test script creation and execution environment for nexo standards adopters
- Implements official nexo specifications (Acquirer & TMS v6.0, NIS V4.0)
- Include test plans nexo-IS 4.0
- Available test solutions:
- nexo Acquirer test solution
- nexo POI test solution
- Based on the black-box testing principle, our solution provides protocol simulators:
- nexo Acquirer protocol
- nexo TMS protocol
- nexo Retailer protocol
Support for all phases of your testing project
Test creation
- Create test cases within the tool using the features of the GUI. User defines what they expect to happen, select Data to be used, define additional validations if required.
Test case management*
- Create and manage test cases within the tool, organize them into libraries and build regression or certification test sets that ensure reproducibility and stability of test quality.*
Test execution & verdict
- Execute tests right from your test case library. Tool generates test messages and responses as defined in the test cases, and makes a test verdict automatically
Automatic payment validation
- Verify system processing, fully automatically, both against format specification and custom, user-built validations
Detailed logging and flexible reporting
- Analyse test results and troubleshoot your system thanks to detailed logs. Generate report of your test campaign thanks to a flexible GUI
Testing against nexo standards specifications
- Powerful message engine implements all rules of the network
- Simulator always up-to-date with maintenance
- Build correct and incorrect messages towards the system under test
- Default format validation uses Specification and (if applicable) XSD validation rules to provide detailed information on any errors
- Automated validation of the received message
– Message structure (e.g. Correct fields, order of fields)
– Check for mandatory and optional fields
– Check conditional fields
– Check each field against format
– Value sets validation
- Report all detected errors in a friendly manner to help resolve the issue
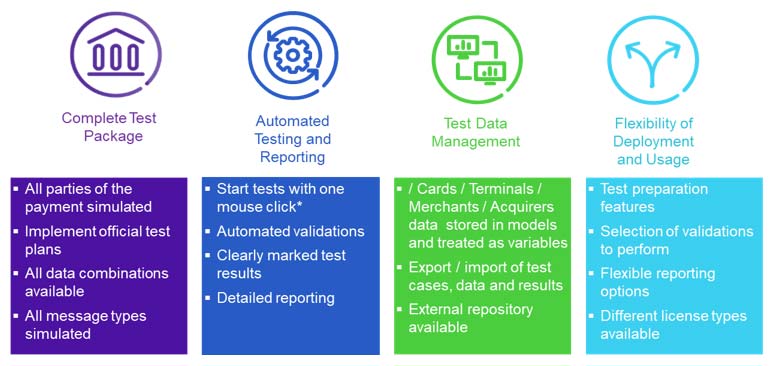
Benefits
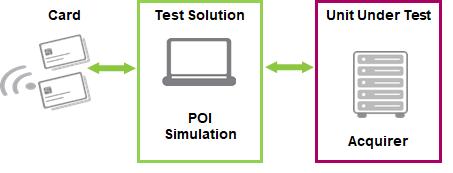
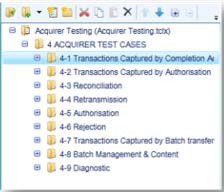
NEXO ACQUIRER TEST SOLUTION
Features
- Simulates POI to put Acquirer Host under test
- Implements test cases of nexo-IS 4.0 test plan
- Qualified by nexo Standards
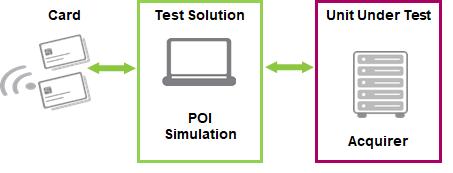
- Dedicated for acquirers and acquirer system providers
- Accredited in June 2019
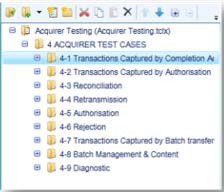
- A set of 120 test scripts implemented (representing 200 test cases in the nexo IS V4.0 Acquirer test plan)
- All Acquirer test scripts are included in the Acquirer test tool library
Steps to Acquirer Host / POI certification
- Obtain nexo IS test Tool from nexo standards
- Test your implementation during the development and testing phase
- Run the official test library in nexo-ISD test tool to pre-certify or validate your solution
- Contact an accredited lab for certification
- Get certified by the certification authority
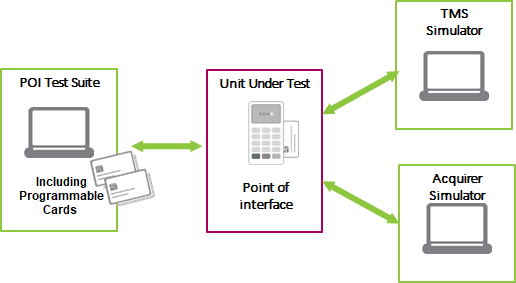
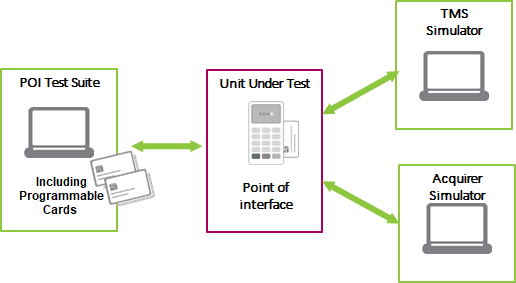
POI TEST SOLUTION
- Dedicated for POI application developers and vendors
- Accredited in June 2020
- A set of 626 test scripts implemented (representing around 950 test cases in nexo IS V4.0 POI test plan) of which:
- 171 are mandatory
- 140 are required for French and German markets
- 7 are for unattended only
- 18 are for combined readers
- 290 are for optional services and features that could be selected in the Vendor’s POI ICS
- All POI test scripts are included in the POI test tool library
- All test cases are included in tool
- Applicable test cases for each POI under test defined by filling in the Implementation Conformance Statement file (ICS)
- The content and layout of the file is defined by nexo
- The tool allows
- loading ICS file to select applicable test cases
- defining ICS by filling in a questionnaire
- Based on content of ICS, test cases are disabled/enabled for execution
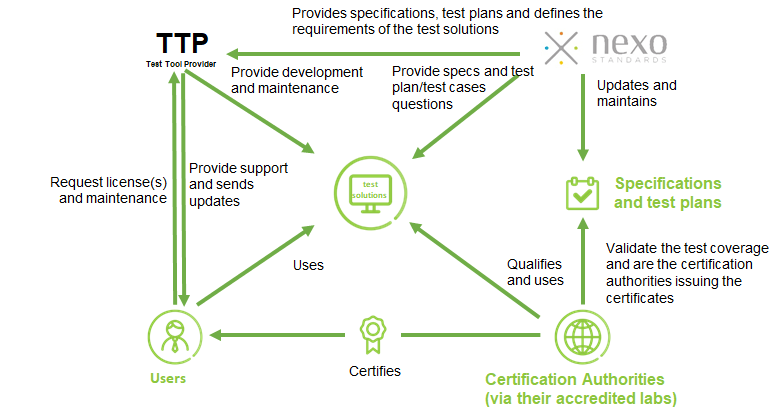
CERTIFICATION FRAMEWORK
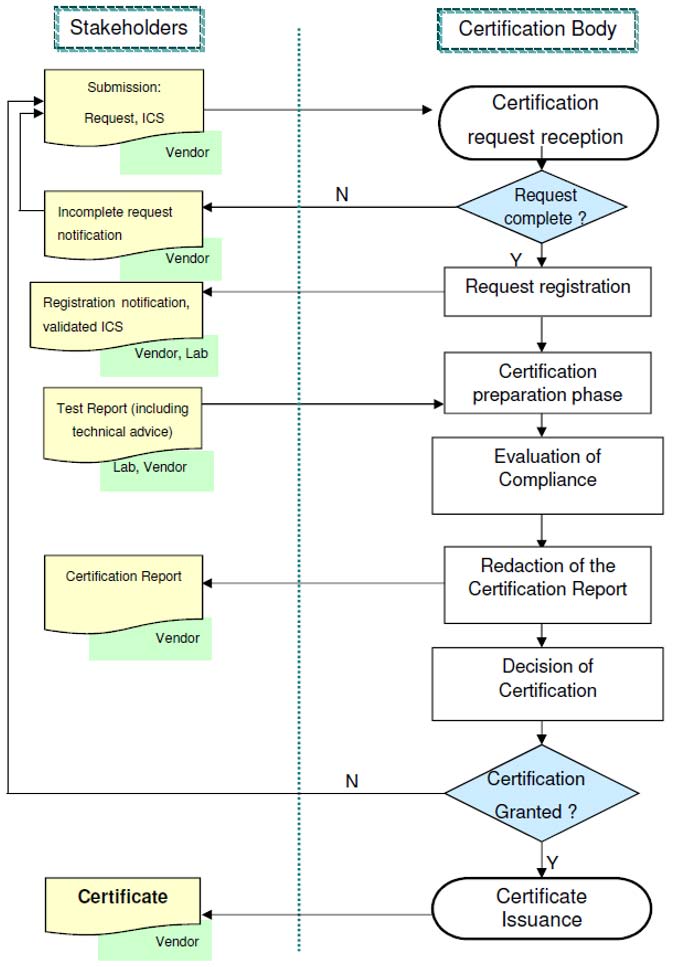
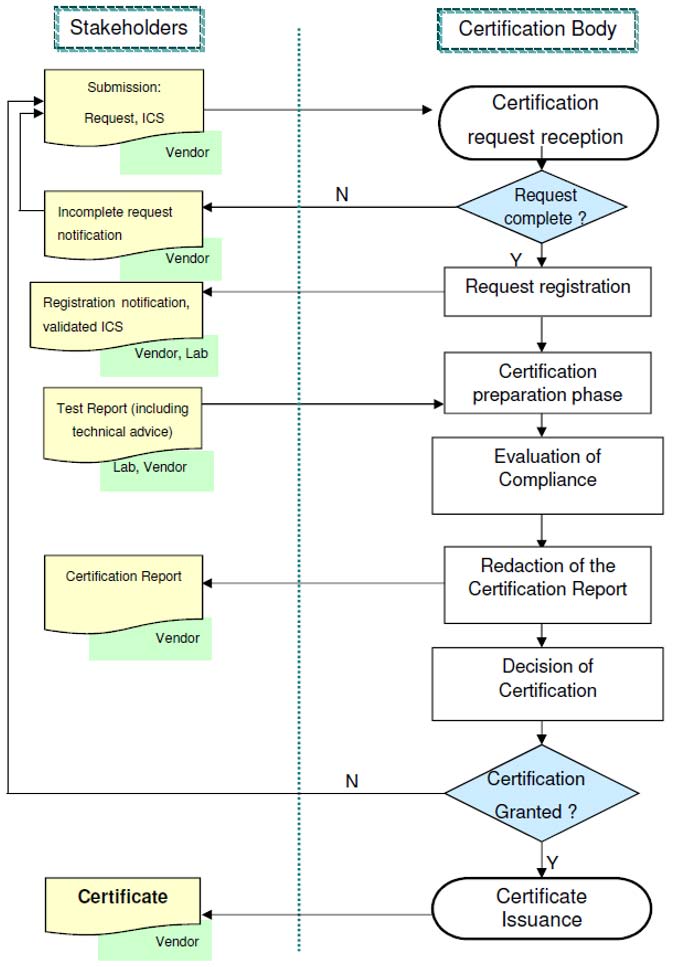
Nexo standards and CFCF (the Common Functional Certification Framework) have signed a Liaison agreement to cooperate in order to provide for the certification of products having implemented nexo specifications
The CFCF certification infrastructure enables a test and certification process of nexo solutions. The governance of the certification process runs by the members of the CFCF. The test and certification process is based on the principle of consensus-based decisions between the members of the CFCF who would like to base their approvals on the CFCF certification process using nexo implementation specifications. The certification infrastructure shall be maintained and enhanced in order to make it available as a general service to interested Approval Bodies. CFCF defined its certification policy in a dedicated documentation which can be found under http://www.cfcf.eu/certification-process/.
The CFCF Certification process covers the functional Test and Certification Policy applicable to POI and acquirer systems developed following the nexo Implementation Specification developed and maintained by nexo standards
The CFCF infrastructure involves :
- Certification Applicants (Vendors),
- Test Laboratories
- Certification Bodies and
- The Certification Committee
These parties roles are based on the usage of the nexo Implementation Specification, the nexo Test Specification as well as on the test methodology and the administrative process agreed within CFCF. The Certification Bodies produce Certificates, which will be used by the Approval Bodies as part of Type Approval. Based on the common specification, the common test specification, a common test methodology and common certification processes, the CFCF certification infrastructure provides for a “one-stop-shopping” for all nexo compliant solutions. A certificate based on one single test report can be used by Approval Bodies as part of Type Approval.
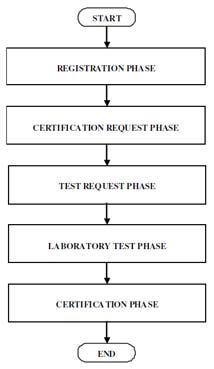
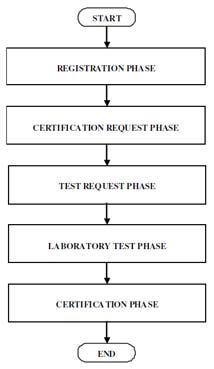
CERTIFICATION PROCESS